Enterprise grade data protection to keep your data safe
End to End Security
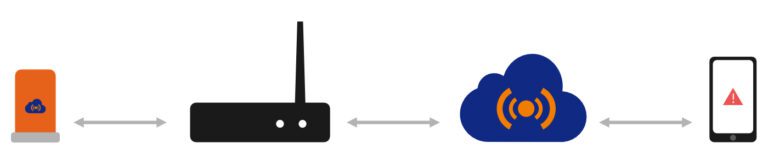
Enterprise grade security keeps your data safe during transmission and storage on the cloud.
SENSOR
- TSCH protocol with AES 256 encryption
- Secure communication from sensor to gateway
- Secure communication from sensor to mobile app
IOT GATEWAY
- TLS 1.2 secured communication with cloud
- x.509 device side certificate
- Crypto engine for secure boot and key storage
- User authorization for devices management
- Firewall
- Gateway initiated outbound connections only

IOEYE PREDICT CLOUD
- ISO 27001 compliant AWS datacenter
- TLS 1.2 secured communication
- Two factor authentication
- Controlled and audited access
- All sensitive data encrypted during storage
Strong security measures to keep your data safe
Authentication
Strong authentication ensures that only the right people access your data. Features such as single sign-on, two-factor authentication and flagging suspicious login activity.
Device Security
Secure encrypted communication between sensor to gateway, mobile or cloud. Cryptographic accelerator with secure hardware-based key storage and identity management on Gateways.
Secure Application
We perform server penetration tests, in-depth testing for vulnerabilities inside the application.
Data Protection
Sensitive data, like passwords, is encrypted or hashed. Insights and complete audit trails into actions take.
Data Loss Protection
All data is mirrored and regularly backed up off site.
Data Center Security
Our application is hosted in secure AWS datacenter. Our database servers are hosted on virtual private network and not accessible over the internet.